Google, GTIG and Mandiant disrupt suspected China-linked UNC2814 GRIDTIDE cyber espionage campaign after 53 breaches across 42 nations.

Google’s Threat Intelligence Group (GTIG), in collaboration with Mandiant and other industry partners, has disrupted the infrastructure of a long-running cyber espionage campaign attributed to a suspected China-linked threat actor tracked as UNC2814. The group has been active since at least 2017, targeting organisations across the globe.
According to the joint report, UNC2814 is believed to have breached at least 53 organisations spread across 42 countries, including government agencies and telecommunications companies in Africa, Asia, the Americas and other regions. Some suspected infections may extend into 20 or more additional countries.
A defining feature of the campaign was the use of a novel backdoor malware dubbed “GRIDTIDE,” which abused the Google Sheets API as a covert command-and-control (C2) channel. By using legitimate cloud services in this way, UNC2814 was able to mask malicious traffic as normal user activity, enabling persistence and stealth within compromised environments.
GTIG and partners took decisive action to dismantle the group’s infrastructure by terminating attacker-controlled Google Cloud projects, disabling compromised accounts and API access, and shutting down known malicious infrastructure. Affected organisations have received formal notifications, and Google is providing support to help with remediation and recovery.
Despite the widespread compromise, Google noted that it did not observe confirmed data exfiltration during the disruption. However, the extent of access gained in some cases involving systems containing personally identifiable information, underscores the severe risks posed by advanced persistent threats.
Cybersecurity experts warn that the disruption highlights ongoing risks associated with attackers leveraging trusted cloud services to conceal their operations. The action against UNC2814 also demonstrates the growing role of industry-level threat intelligence collaboration in identifying and mitigating sophisticated global cyber threats.
Reports are sourced from official documents, law-enforcement updates, and credible investigations.
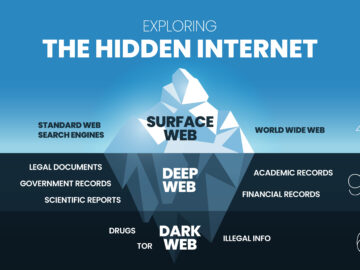
Discover additional reports, market trends, crime analysis and Harm Reduction articles on DarkDotWeb to stay informed about the latest dark web operations.