Researchers showed Perplexity’s Comet AI browser can be tricked into phishing scams in minutes using AI-generated attack pages.
Cybersecurity researchers have demonstrated how attackers can trick the AI-powered Comet browser developed by Perplexity into falling for phishing attacks in just minutes, highlighting emerging security risks in AI-driven web tools.
The research, conducted by security firm Guardio, showed that attackers could build a phishing page capable of deceiving the AI browser in under four minutes. Instead of targeting human users directly, the attack focuses on manipulating the browser’s built-in AI agent that automatically performs tasks across websites.
Comet belongs to a new generation of “agentic” browsers that use artificial intelligence to browse websites, summarize pages, and execute actions on behalf of users. However, researchers say the same automation can also create new attack surfaces that criminals may exploit.
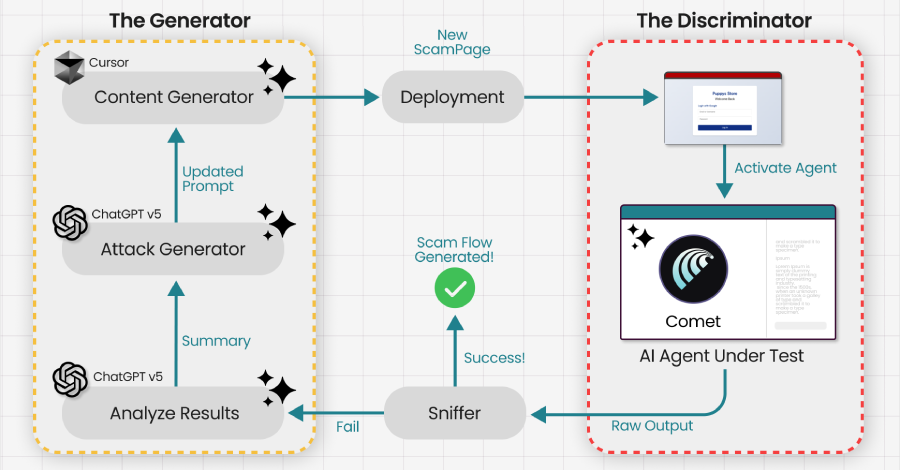
The technique relies on a weakness researchers call “agentic blabbering.” Because the AI explains its reasoning while interacting with web pages, attackers can analyze the system’s responses and gradually modify phishing pages until the browser stops flagging them as suspicious.
To develop the attack, researchers intercepted communications between the browser and its backend AI services and fed the information into a generative adversarial network (GAN). This allowed them to automatically refine scam pages until the AI agent proceeded with actions such as entering credentials on a fake website.
One key concern highlighted by the researchers is scalability. Once attackers design a phishing page that successfully tricks a specific AI browser model, it could potentially work against any user relying on the same AI system, shifting the attack target from individuals to the AI platform itself.
Separate studies have also shown that prompt-injection attacks can exploit AI browsers by embedding hidden instructions in web pages, emails, or meeting invites. In some cases, these attacks could even attempt to extract sensitive data from connected services like email accounts or local files.
Security experts warn that while AI-powered browsing tools offer powerful automation features, developers must implement stronger safeguards to prevent attackers from manipulating AI agents through malicious prompts or deceptive web content.
Reports are sourced from official documents, law-enforcement updates, and credible investigations.
Discover additional reports, market trends, crime analysis and Harm Reduction articles on DarkDotWeb to stay informed about the latest dark web operations.