NASA employees were duped in a years-long phishing campaign by a Chinese national posing as a US researcher.
USA, April 24, 2026 – NASA employees were among multiple victims of a long-running phishing campaign orchestrated by a Chinese national who impersonated U.S. researchers to obtain sensitive aerospace and defense-related software.
The scheme, revealed by NASA’s Office of Inspector General, ran from January 2017 to December 2021, targeting not only NASA but also U.S. military branches, government agencies, universities, and private companies.
Key individuals
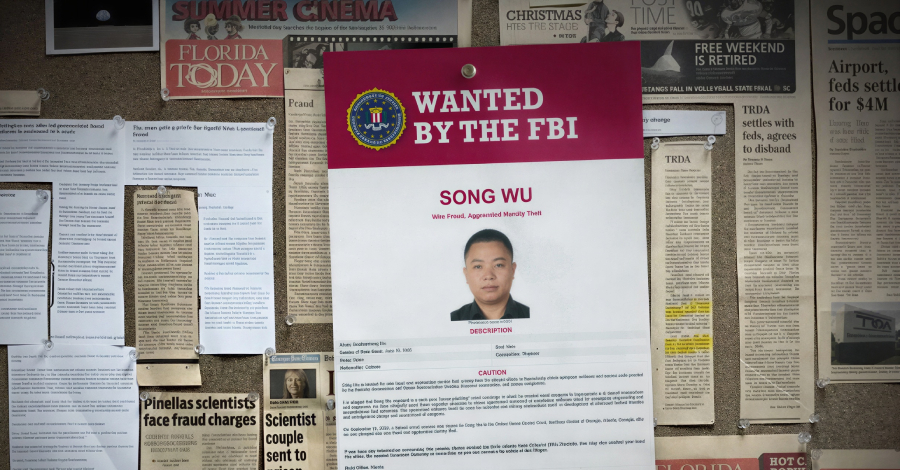
- Song Wu (40) – Alleged orchestrator of the phishing campaign, posing as U.S. researchers
- NASA employees and collaborators – Victims who unknowingly shared sensitive software
- U.S. Department of Justice – Filed charges including wire fraud and identity theft
According to investigators, the attacker created fake identities impersonating legitimate U.S. engineers and academics. By building trust with targets, he convinced them to share export-controlled aerospace software and source code, believing they were collaborating with colleagues.
The individual behind the operation was identified as Song Wu, an engineer linked to the state-owned Aviation Industry Corporation of China (AVIC). Prosecutors allege he conducted extensive research on targets and repeatedly requested access to proprietary software used in aerospace design and weapons development.
Authorities said the campaign succeeded in several cases, with victims unknowingly transferring sensitive technology that could have military applications. The stolen software is believed to be relevant to aircraft design and advanced weapons systems.
Wu was indicted in 2024 on charges including wire fraud and aggravated identity theft. If convicted, he faces up to 20 years in prison per wire fraud count, along with additional penalties. He is currently believed to remain at large.
Officials warned that the case highlights the effectiveness of long-term social engineering campaigns, where attackers exploit trust rather than technical vulnerabilities to access sensitive data.
Related articles :
- ZeroDayRAT Mobile Spyware Steals Data, Enables Surveillance
- FBI Warns Russian Hackers Target Signal, WhatsApp
- Europol Operation Dismantles Tycoon 2FA Phishing Network
Reports are sourced from official documents, law-enforcement updates, and credible investigations.
Discover additional reports, market trends, crime analysis and Harm Reduction articles on DarkDotWeb to stay informed about the latest dark web operations.